TL;DR: Lorikeet Security provides two products that work together to give organizations complete security coverage. Attack Surface Management (ASM) continuously discovers and monitors your external footprint -domains, subdomains, IPs, technologies, emails, and code repositories -using a multi-phase scanning engine with AI-powered enrichment. Penetration Testing as a Service (PTaaS) delivers expert-led, 100% manual penetration testing through a modern portal with digital contract signing, real-time finding delivery, and compliance-ready reports. This guide walks through every feature of both products, shows the actual platform interfaces, and explains why modern organizations need continuous monitoring and deep manual testing working in tandem.
Most organizations discover they have a security problem in one of two ways: they get breached, or they hire someone to try. The first option is catastrophic. The second option -penetration testing -has been the gold standard for decades, but the way it has traditionally been delivered is fundamentally broken for the pace at which modern organizations operate.
We built the Lorikeet Security platform to solve both problems simultaneously. Our Attack Surface Management product provides continuous, automated discovery and monitoring of your external footprint. Our Penetration Testing as a Service portal delivers expert-led assessments through a modern, transparent workflow. Together, they give organizations both the breadth of continuous monitoring and the depth of manual expert analysis.
Part 1: Attack Surface Management
Your attack surface is everything an attacker can see about your organization from the outside. The problem is that most security teams only know about a fraction of what is actually exposed. Shadow IT, forgotten development servers, legacy subdomains, and third-party integrations create blind spots that attackers exploit routinely.
Lorikeet ASM solves this by continuously scanning, cataloguing, and monitoring every asset tied to your organization. When something new appears, changes, or becomes vulnerable, you know about it -not during your next annual pentest.
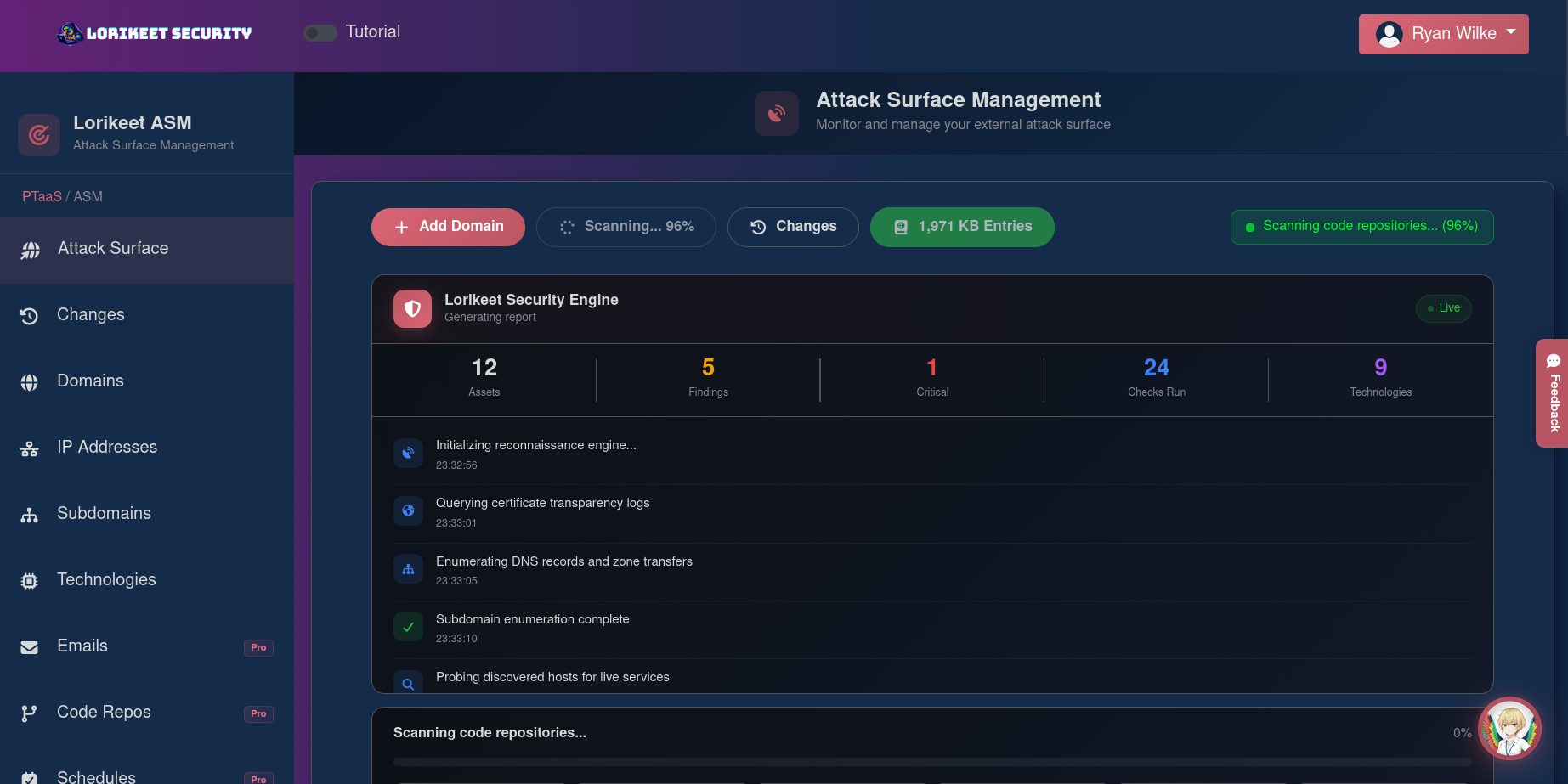
The ASM scanning dashboard during an active scan -the Lorikeet Security Engine runs through reconnaissance, discovery, fingerprinting, and vulnerability analysis in real time.
The Multi-Phase Scanning Engine
The Lorikeet scanning engine operates in six distinct phases, each building on the results of the previous one. This is not a simple port scan or DNS lookup -it is a comprehensive, methodical process that mirrors how an actual attacker would perform reconnaissance against your organization.
Recon
DNS brute-forcing across 110+ prefixes, certificate transparency logs, HackerTarget, ThreatCrowd, BufferOver, and SecurityTrails APIs.
Discovery
Live host probing with headless browser screenshots of every accessible service via Puppeteer integration.
Fingerprinting
Technology detection via HTTP headers, favicon hashing, and response patterns -servers, frameworks, CMS, JS libraries.
Vuln Analysis
Security headers, outdated libraries, cookie issues, SSL/TLS, SPF/DKIM/DMARC, open ports, CORS misconfigurations.
Exploit Validation
AI-assisted exploitability verification with confidence scoring to eliminate false positives.
Report Generation
Findings enriched from 1,969+ KB entries (OWASP ASVS/WSTG/Top 10, MITRE CWE/CAPEC) with CWE mapping and remediation.
Why this matters: Many ASM tools are just automated Nmap scans with a dashboard. Our multi-phase approach replicates attacker methodology -the same progression from reconnaissance to exploitation that a real adversary follows. The findings you see are the same findings an attacker would find.
What Gets Discovered and Monitored
The ASM dashboard organizes your attack surface into six asset categories, each continuously updated as scans run:
Domains
Root domains with verified ownership, subdomain counts, DNS health, and certificate monitoring.
Subdomains
Every subdomain via DNS, CT logs, and OSINT -with parent linkage and live/dead status.
IP Addresses
IPv4/IPv6 with PTR records, ASN info, geolocation, and associated services.
Technologies
Complete fingerprinting -servers, frameworks, CMS, JS libraries with version and CVE mapping.
Emails
Exposed addresses from OSINT, breach databases, and scraping -with source tracking.
Code Repos
GitHub, GitLab, Bitbucket scanning for secrets, API keys, and sensitive config files.
Findings, Severity, and Remediation

The ASM analytics view with severity breakdown, finding status, top technologies detected, recent activity timeline, and Lory AI providing a real-time attack surface summary.
Every vulnerability discovered by the scanner is classified by severity (Critical, High, Medium, Low, Informational) and tracked through a status workflow: Open → In Progress → Resolved, with additional states for False Positive and Accepted Risk. Each finding includes a clear title and description, affected asset URL, evidence (screenshots, HTTP responses, proof), CWE mapping for standardized classification, and specific remediation guidance sourced from the knowledge base.
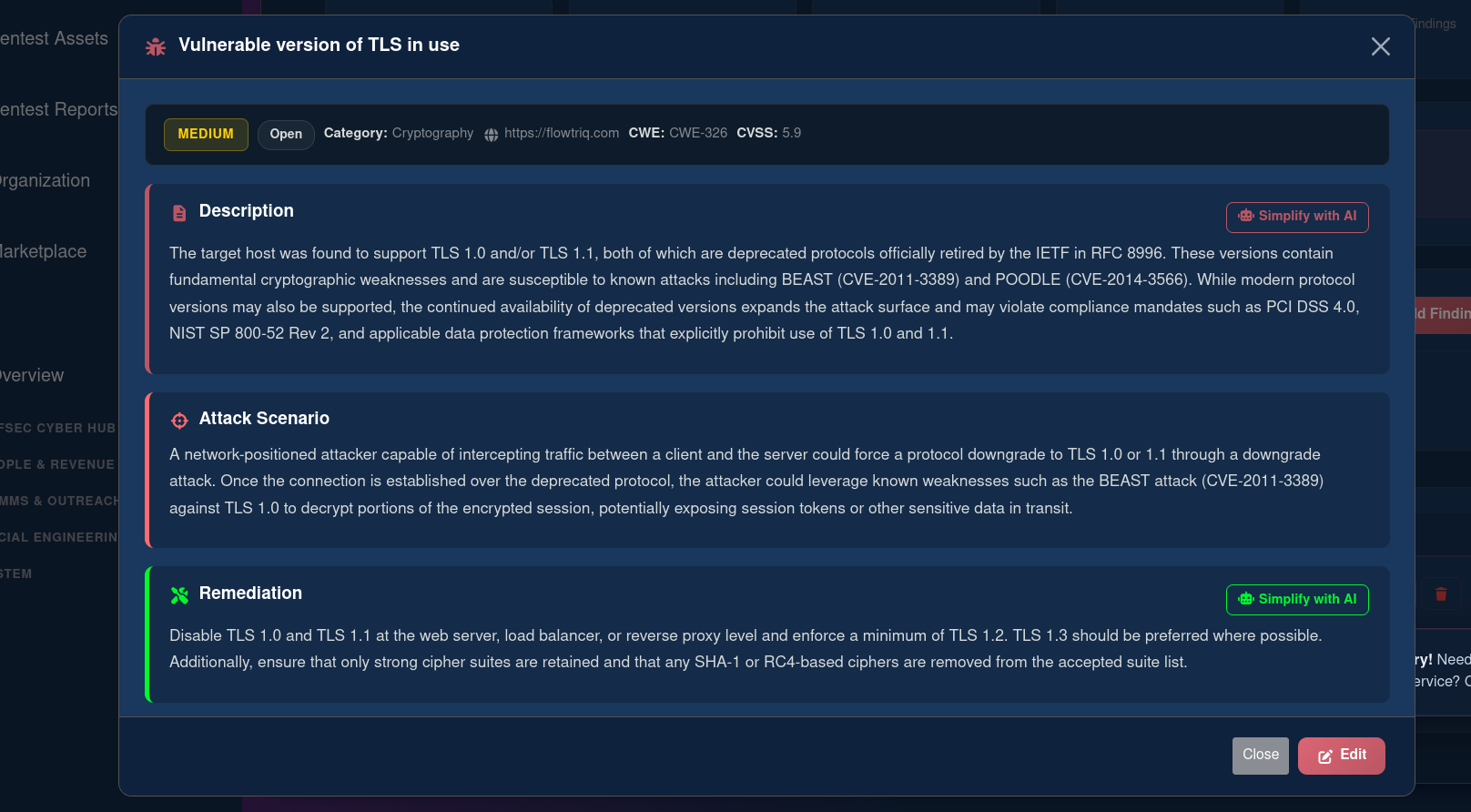
A finding detail view from the PTaaS portal showing description, attack scenario, and remediation with "Simplify with AI" for board-ready risk summaries.
Lory: AI-Powered Security Intelligence
Integrated into the ASM dashboard is Lory, our AI security assistant. Lory is deeply integrated with your live findings data and can answer natural language questions about your attack surface. Ask "summarize my attack surface" and it provides an overview of your monitored domains, discovered subdomains, technologies in use, and total findings. Lory also powers AI Risk Simplification -converting technical vulnerability descriptions into board-ready business risk assessments with financial exposure estimates, likelihood of exploitation, and recommended priority.
Continuous Monitoring and Change Detection
ASM is not a one-time scan. The platform supports scheduled scans (daily, weekly, or monthly) and maintains a real-time change log tracking new assets, configuration changes, removed assets, and newly discovered vulnerabilities. This is critical because your attack surface is never static -developers deploy services, DNS records change, certificates expire, and every change can introduce new risk.
Part 2: Penetration Testing as a Service
Penetration testing has been the most effective way to identify real security vulnerabilities for decades. The methodology is sound: hire experienced security researchers to think and act like attackers, find the weaknesses that automated tools miss, and deliver actionable findings. The problem has never been the testing -it has been the delivery model.
The Problem with Traditional Pentesting
You email a vendor. They send a questionnaire. You wait. They send a proposal. You negotiate. You sign a contract via DocuSign. You wait again. Testing happens behind a curtain with zero visibility. Weeks later, a 200-page PDF lands in your inbox. By then, your codebase has changed, your infrastructure has shifted, and some findings are already outdated.
This model worked in 2005 when organizations deployed software quarterly. It does not work in 2026 when teams deploy multiple times per day.
How Lorikeet PTaaS Works
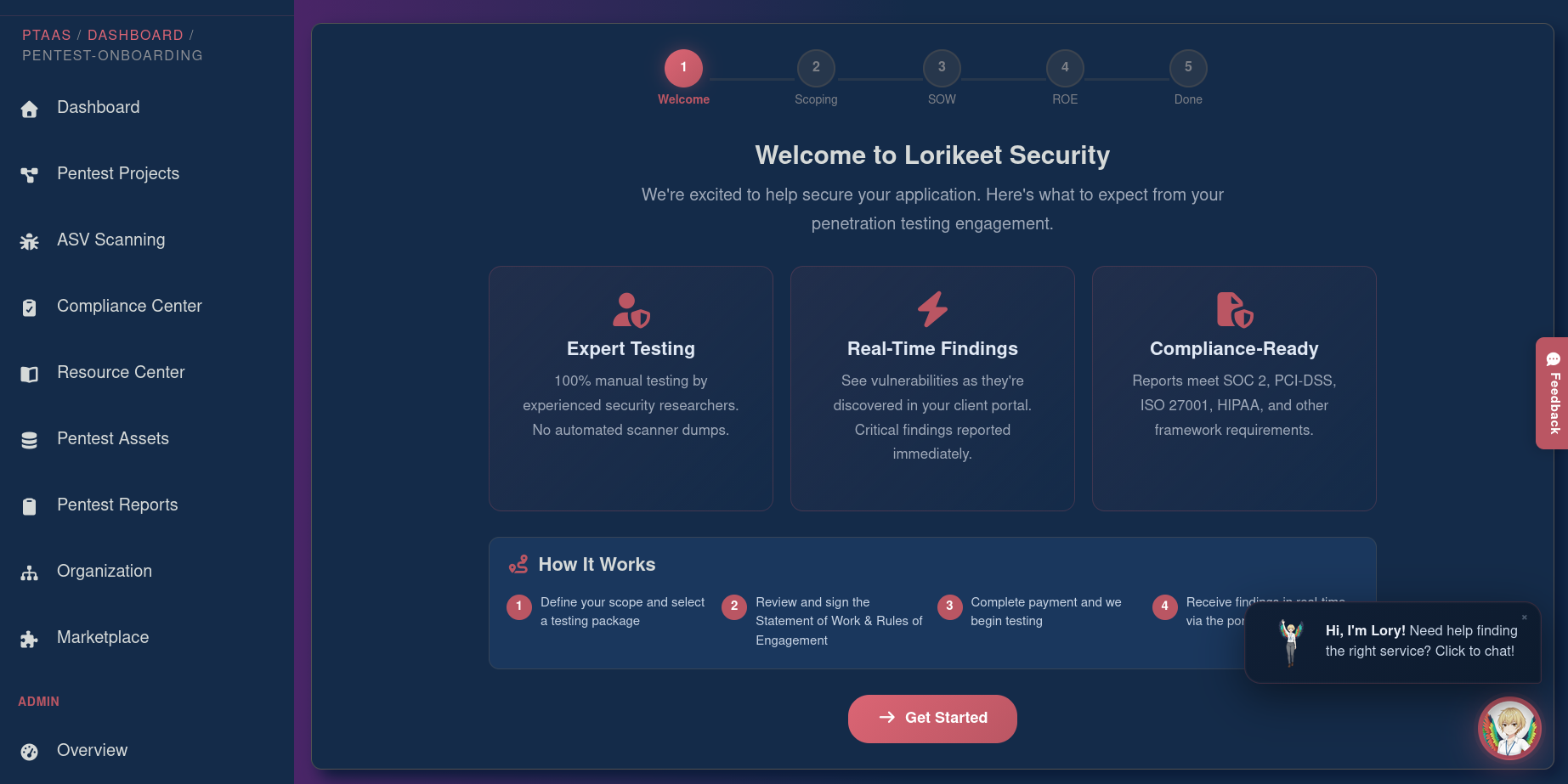
The PTaaS portal onboarding wizard -a guided 5-step workflow from scoping through contract signing, with feature highlights and the "How It Works" guide.
The Lorikeet PTaaS portal replaces the entire traditional workflow with a modern, self-service experience:
Scope Your Engagement
Select your project type, specify target assets, choose testing dates, and upload supporting documentation -all directly in the portal. No email chains, no questionnaires.
Sign Contracts Digitally
Review the auto-generated Statement of Work and Rules of Engagement in a scrollable viewer, then sign with the embedded signature pad. No DocuSign, no wet signatures, no PDF roundtrips.
Track Real-Time Findings
Findings are delivered as they are discovered -not weeks later in a PDF. When a tester finds a critical vulnerability on day one, you see it on day one. Your team can start remediating immediately.
Download Your Report
Executive and technical report formats with compliance mappings for SOC 2, PCI-DSS, ISO 27001, and HIPAA. Reports are pushed to your portal and downloadable instantly.
Testing Types We Offer
We support 15 types of expert-led penetration testing through the portal -each scoped and delivered through the same streamlined workflow:
The Project Dashboard
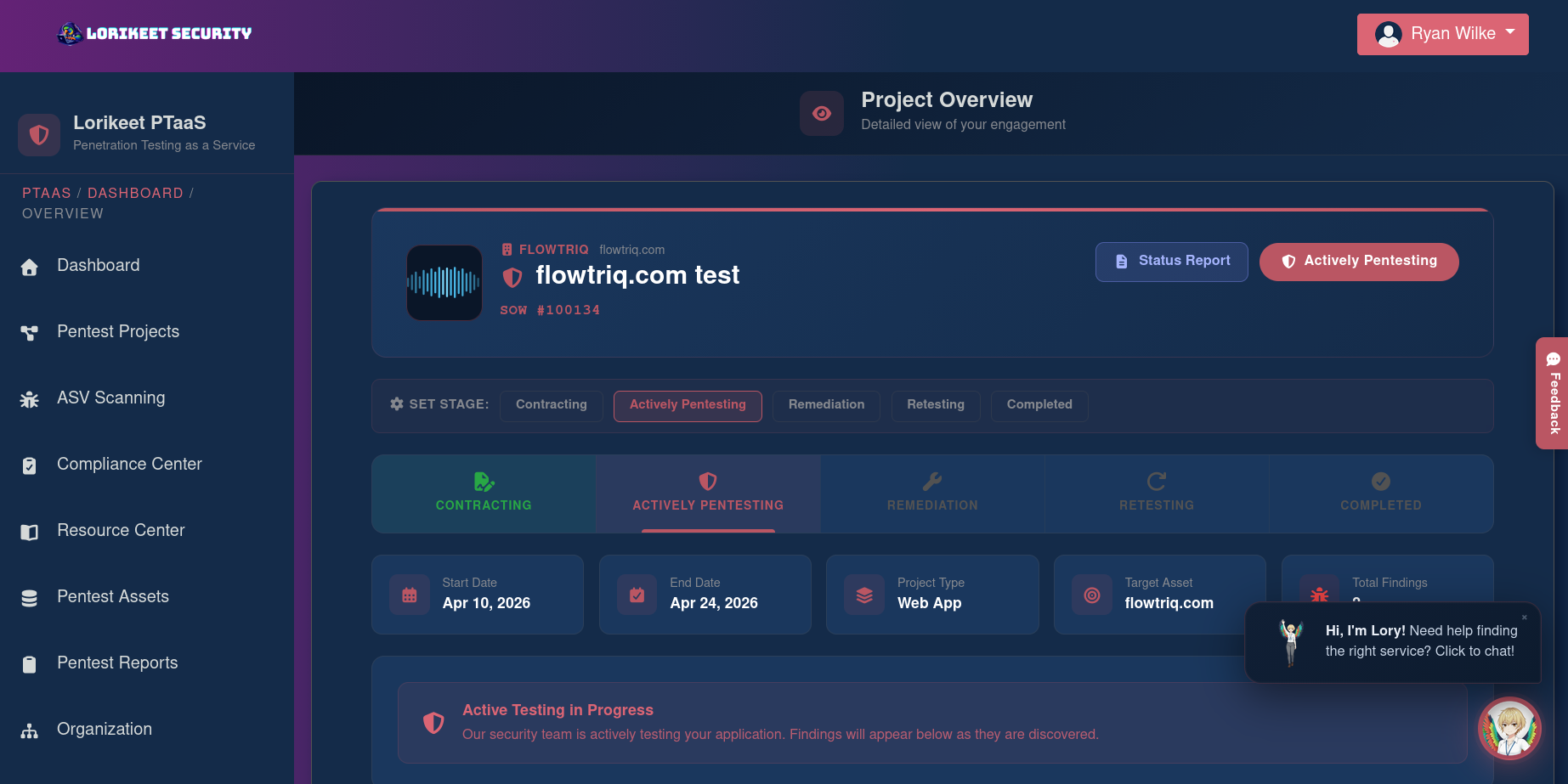
A live pentest engagement in the PTaaS portal. The five-stage pipeline tracks progress from contracting through completion, with project details and real-time status.
Each finding includes a severity rating, detailed description with reproduction steps, affected assets, evidence (screenshots, HTTP requests/responses, proof-of-concept code), CWE classification, and step-by-step remediation guidance. Findings can be filtered by severity, status, and category.
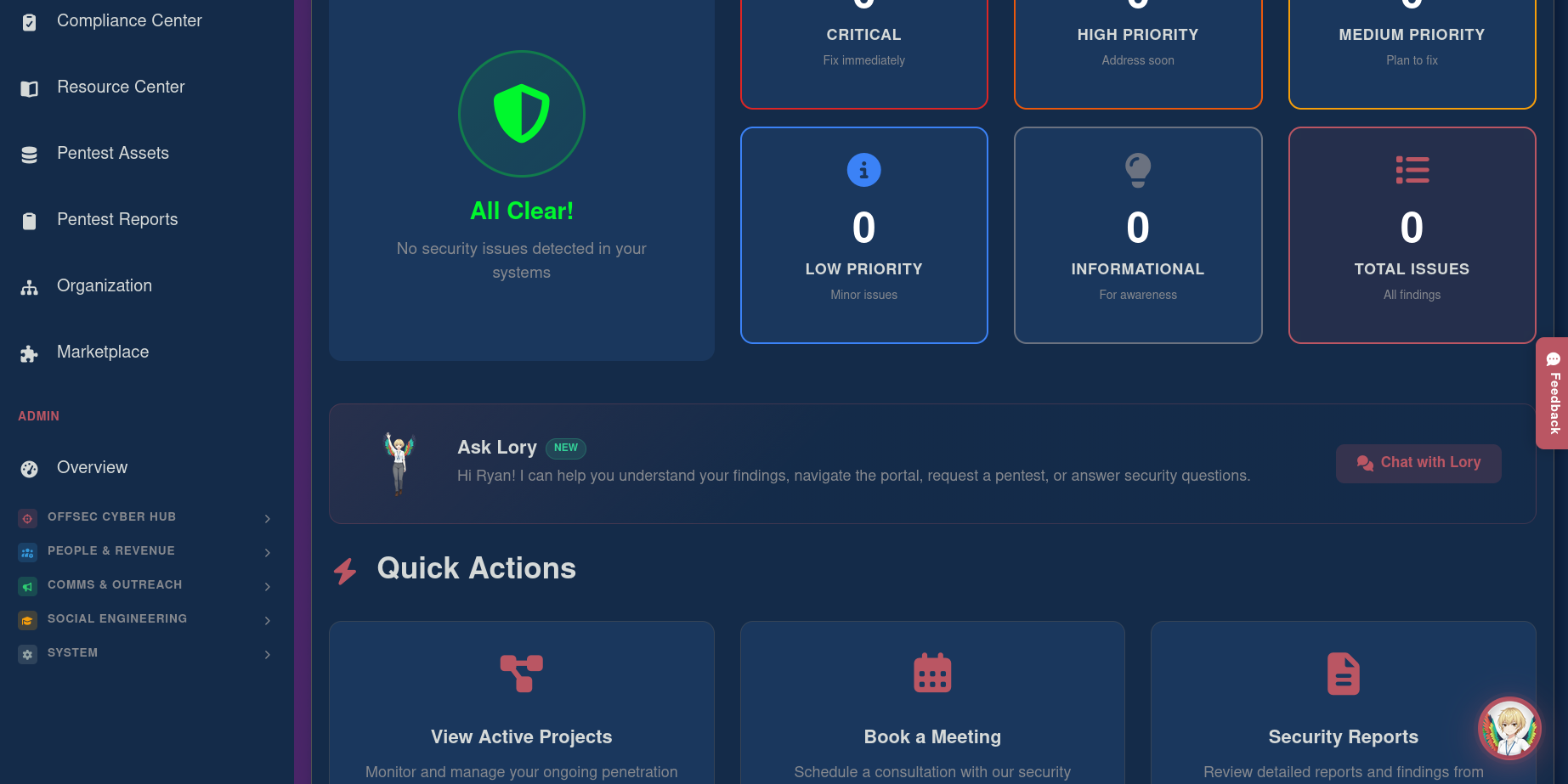
The PTaaS client dashboard with security status overview, Lory AI assistant, and quick actions for managing your engagement.
Reporting and Compliance
Final reports include an executive summary for leadership, detailed methodology, every finding with evidence and remediation steps, attack path narratives showing how findings chain together, a prioritized remediation roadmap, and compliance mappings to SOC 2, PCI-DSS, ISO 27001, and HIPAA.
Want to see what a report looks like? We publish a full demo penetration testing report so you can review our format, depth, and quality before engaging.
Compliance note: Every Lorikeet pentest report satisfies SOC 2 Trust Services Criteria (CC4.1, CC7.1), PCI-DSS Requirement 11.3, ISO 27001 Annex A.8, and HIPAA Security Rule administrative safeguards. Your report is audit-ready out of the box.
PTaaS vs. Traditional Penetration Testing
The difference is not the testing -it is everything around it. Same caliber of researchers, same methodologies. The difference is the delivery model, the transparency, and the speed:
| Aspect | Traditional Pentesting | Lorikeet PTaaS |
|---|---|---|
| Scoping | Email exchanges, questionnaires, phone calls over days/weeks | Self-service portal -scope and start in minutes |
| Contracting | PDF contracts via DocuSign, legal review cycles | Digital SOW + ROE signed in-browser with signature pad |
| Visibility | Zero visibility -"black box" vendor relationship | Real-time dashboard with live findings as they are discovered |
| Findings | Delivered weeks later in a monolithic PDF | Appear in portal immediately with severity, evidence, remediation |
| Remediation | Fix from static PDF, request retesting separately | Track status in portal, retesting included |
| Reports | Template-heavy PDF with automated scanner output | Executive + technical formats, compliance-mapped, downloadable |
| Quality | Varies -may be partially automated | 100% manual by experienced researchers. No scanner dumps. |
| Retesting | Separate engagement, additional cost | Included in engagement workflow |
| Timeline | 4–8 weeks from inquiry to report | Engagements begin within days of signing |
Compliance Integration: GRC Dashboard
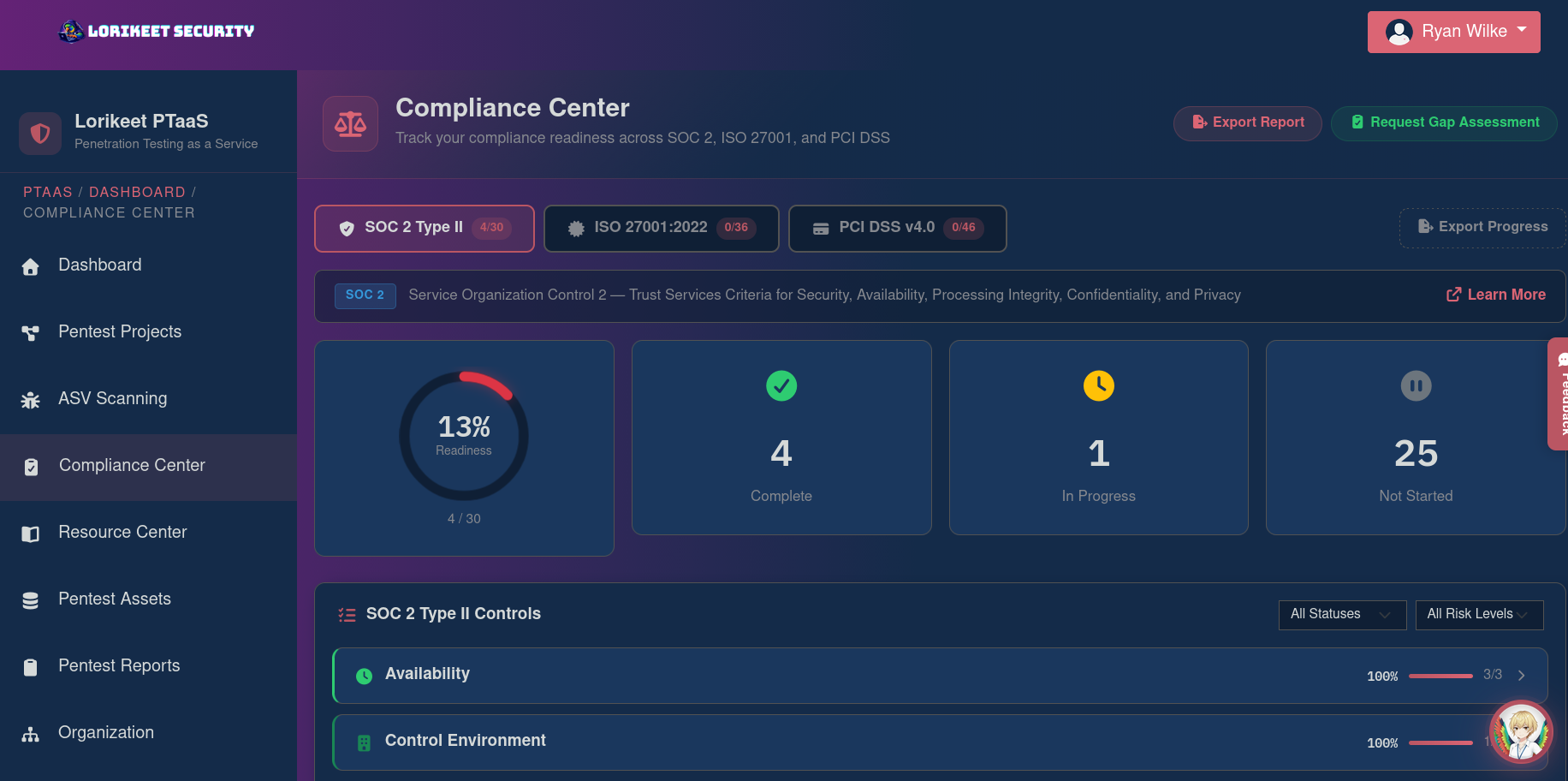
The Compliance Center with SOC 2 Type II, ISO 27001, and PCI-DSS framework tracking, readiness scoring, and per-control status management.
The platform includes a Governance, Risk, and Compliance dashboard mapping your security posture to SOC 2 Type II, ISO 27001:2022, and PCI-DSS. It provides cross-framework control mappings, evidence upload via secure S3 storage, and AI-powered compliance guidance through Lory. Your pentest findings, ASM discoveries, and compliance evidence all live in one platform.
Why Organizations Need Both ASM and Pentesting
ASM provides breadth. It continuously scans your entire external footprint, discovers unknown assets, identifies configuration issues at scale, and alerts on changes. It answers: what is exposed?
Pentesting provides depth. It manually tests specific targets with adversarial intent, finds business logic flaws automation cannot detect, chains vulnerabilities into realistic attack scenarios. It answers: what can an attacker actually do?
Consider: ASM discovers 47 subdomains, 3 with missing security headers, 1 with an outdated jQuery CVE, 2 with exposed dev endpoints. Valuable. But a pentest discovers the dev endpoint authentication can be bypassed, granting access to an internal API returning customer records, and the XSS can be chained with CSRF to hijack admin sessions. The pentest turns surface-level findings into a complete attack narrative with real business impact.
ASM: Continuous Breadth
Catches issues as they appear. Informs pentest scoping. Verifies remediation persists over time. Satisfies continuous monitoring requirements.
Pentesting: Expert Depth
Finds what automation misses. Chains vulnerabilities into attack paths. Validates security controls under real adversarial conditions. Satisfies assessment requirements.
See It in Action

The ASM product page at lorikeetsecurity.com/asm with live scanning statistics, feature breakdowns, and dashboard previews.
Visit our Attack Surface Management page to see scanning statistics, feature breakdowns, and subscription tiers. We offer three levels: Personal for core scanning and monitoring, Professional which adds AI assistant, AI risk analysis, and marketplace integrations, and Company / Enterprise with the full feature set including unlimited domains, priority scanning, and dedicated support.
For pentesting, visit our PTaaS portal to see the onboarding flow, feature overview, and the step-by-step guide: select your scope, sign contracts, track real-time findings, and download your compliance-ready report.
See a Real Pentest Report
Transparency is core to how we work. Preview an example deliverable so you know exactly what to expect.
Ready to See Your Attack Surface?
Start with Attack Surface Management for continuous monitoring, or book a penetration test for deep manual analysis. Both start with a simple conversation.

